Your Network Didn’t Fail All at Once. It Started Leaking Certainty.
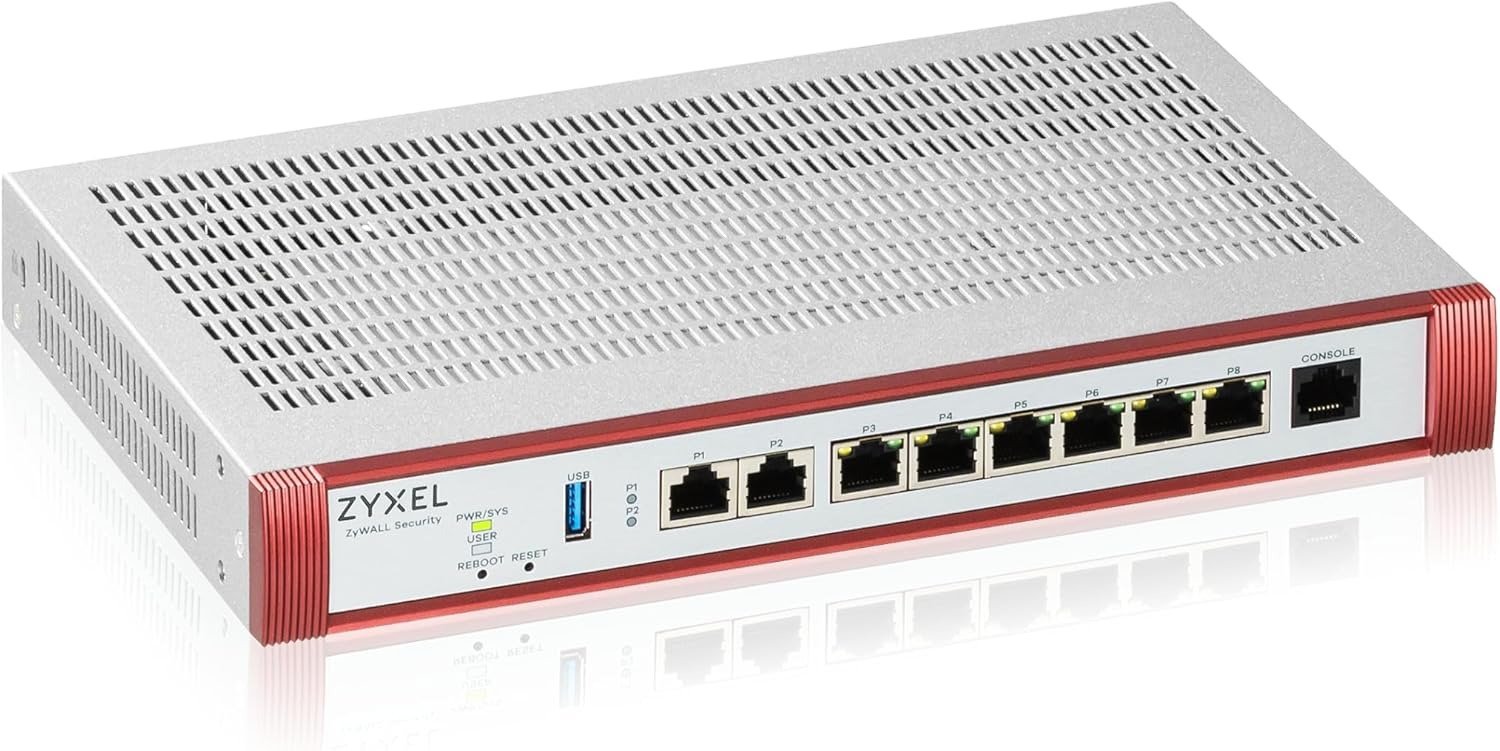
ZYXEL USG FLEX 200H
You usually do not notice the real problem when a network is still “working.”
The video call still connects. Files still move. Staff still log in. The dashboard looks calm enough. Then one more thing gets switched on—inspection, remote access, a few VLANs, maybe heavier traffic from cameras or cloud apps—and the whole environment changes character. Not dead. Worse. Sluggish, brittle, unpredictable.
That is the part most buyers misread.
They shop for a firewall the way people shop for a lock by staring at the paint. Port count, headline throughput, brand comfort. Meanwhile the real decision is hiding somewhere else: what happens when security is no longer decorative and traffic is no longer light?
That is the threshold this product is built around.
What pulled me into the Zyxel USG FLEX 200H was not the usual marketing language. It was the shape of the compromise it is trying to prevent: a small or mid-size office that has outgrown consumer-grade logic, but is not yet willing to pay enterprise tax just to stop second-guessing its edge security. Zyxel positions the 200H for up to 100 users, with 6.5 Gbps SPI firewall throughput, 1.8 Gbps UTM throughput, and 1.2 Gbps VPN throughput, plus two 2.5GbE ports and six 1GbE interfaces. The bundle linked here adds a 1-year Gold Security Pack, which turns on the advanced services many buyers forget to price in at the start.
The Result Looks Fine. The Problem Isn’t.
I have seen this pattern too many times to trust “it seems fine.”
A firewall can pass the casual eye test and still be the quiet source of friction in the building. Not because it is broken, but because it is being judged too early, under too little load, with too few services active. That is how regret walks in wearing a clean shirt.
With the USG FLEX 200H, the first thing that matters is not the box itself. It is the fact that Zyxel designed this H-series around higher-performance UTM and VPN workloads, using a newer hardware and software base, with faster boot behavior, improved CPU performance, and cloud/on-prem management flexibility through Nebula.
What that means in plain English is simple: this is not a vanity upgrade for someone who just wants another blinking box in the rack. It is for the moment when your network edge stops being a passive checkpoint and starts carrying actual operational weight.
What buyers usually look at first
What actually decides the experience later
- Port count
- What throughput survives when security services are active
- “Up to 100 users”
- Whether those users generate inspection, VPN, and policy complexity at the same time
- Base hardware price
- The real cost once IPS, anti-malware, filtering, and reporting are turned on
- “Works today”
- Whether it still feels stable six months later under routine growth
That last row is the one that hurts.
Because the pain is rarely cinematic. It is administrative. A stalled tunnel. A reboot story in the middle of a workday. A team that starts avoiding policies because the edge box feels temperamental. A buyer who thought they had bought capacity, when in reality they had bought delay. Community discussions around the H-series also show the other side of the picture: better performance and a better UI, yes, but also a maturing feature set and some gaps or rough edges still being worked through.
What You’re Actually Feeling but Not Naming
Most people do not say, “My firewall is under-specced for inspected multi-service traffic.”
They say something messier.
They say the network feels heavier than it should.
They say remote access is fine until it isn’t.
They say every new rule feels like a negotiation with future problems.
That foggy irritation has a structure.
What you are really feeling is decision drag—the hidden tax that appears when the edge device is no longer confidently ahead of your requirements. Once that starts, every change becomes emotionally expensive. Adding VLANs feels riskier. Tightening inspection feels optional. Remote users become another moving part you secretly resent.
The USG FLEX 200H aims directly at that psychological toll. Not by promising perfection. By giving you more headroom where small-business buyers usually run out of it first: security throughput, VPN throughput, multi-gig WAN/LAN flexibility, and centralized visibility. The Gold bundle also enables cloud sandboxing, anti-malware, IPS, web filtering with 111 URL categories, application visibility, reputation filtering, and SecuReporter-based analytics from the first year, which matters because a firewall without its real security stack active is often just a comforting shape on the shelf.
The Hidden Mechanism Behind the Miss
Here is the misread at the center of this category:
People confuse advertised firewall presence with usable protected throughput.
Those are not the same thing. Not even close.
The mechanism behind disappointment is brutally ordinary. Every useful layer you turn on—IPS, anti-malware, filtering, VPN, segmentation, reporting—adds work. Not abstract work. Real processing work. So the question is not whether a device can route packets under ideal conditions. The question is whether it still feels composed when the network is being treated like a business network instead of a home router with a stern face.
That is where the 200H gets interesting. Zyxel lists 6,500 Mbps SPI throughput, 1,800 Mbps UTM throughput on the spec page, and Amazon’s bundle page cites 2,500 Mbps IPS throughput for the licensed package, along with 1,200 Mbps VPN throughput, 600,000 concurrent sessions, 100 IPSec tunnels, 50 SSL VPN users, and 32 VLANs. Even where vendor pages separate UTM and IPS figures differently, the broader point stays intact: the box is built for inspected traffic, not just naked routing.
That is the hidden variable most people skip.
They compare firewalls like static objects. The real comparison is dynamic: what survives once the network becomes annoying.

The Threshold Where the Outcome Quietly Breaks
This is the governing model of the article: Threshold.
Not variance. Not drift. Threshold.
Because the buying mistake here does not usually come from tiny differences in flavor. It comes from crossing a line and pretending you did not.
The line looks something like this:
You are approaching the threshold when…
Why it matters
- You need multi-gig WAN or want to stop bottlenecking faster internet
- A 2.5GbE-capable edge starts mattering more than marketing comfort
- You expect IPS, anti-malware, filtering, and reporting to stay enabled
- Security stops being a brochure checkbox and becomes sustained load
- You have remote users or site-to-site needs
- VPN throughput and tunnel handling start shaping daily experience
- You are segmenting traffic across VLANs
- Rule count, inspection, and policy logic stop being “simple”
- You run a small office, but with cameras, SaaS, voice, or sensitive data
- “Small” traffic profiles can still be edge-intensive
Below that threshold, almost any respectable box can look clever.
Above it, cheap confidence begins to rot.
That is why the USG FLEX 200H is not really a product for people chasing the lowest entry price. It is for people who have already seen the cost of pretending the edge is simpler than it is.
Why Most Buyers Misread This Too Early
Because they test for comfort, not pressure.
They look at setup. They look at the first login. They look at whether internet comes through and a tunnel forms. Then they declare the problem solved. It feels rational. It is not.
A Gartner Peer Insights review on the USGFLEX200H describes performance and stability as very good in a small/medium environment, specifically noting that it handles multi-gig WAN and VPN traffic well, while also pointing to the learning curve, licensing complexity, and still-maturing cloud-managed features. That mix is more believable than blind praise because it matches the shape of the category: strong hardware intent, genuine operational upside, but not a toy-level learning path.
Amazon’s review snapshot for the bundled unit shows a 4.0/5 average from 15 global ratings, with 52% five-star and 31% four-star, which is solid but not worshipful. One visible review praises setup ease for someone with long firewall experience, especially when the deployment is not trying to do anything exotic. That detail matters. Products like this rarely fail because they lack features on paper. They fail when buyers underestimate the management style they are agreeing to.
So the early misread usually comes in one of three forms:
- “It has enough ports, so I’m covered.”
- “It says up to 100 users, so I’m future-proof.”
- “I can add security features later.”
That third one is the trap.
Because “later” is where a lot of cheap firewall decisions go to bleed.
Who Is Actually Inside This Problem
You are inside this problem if your office is no longer simple, even if it is still small.
That includes the buyer who has:
- a faster internet circuit than their old edge device can gracefully justify,
- remote workers or site links that need to feel dependable rather than merely possible,
- segmented traffic that should stay segmented without turning policy into a daily irritation,
- a stack of security services they actually intend to leave on,
- or a team that will punish every flaky network moment with fresh distrust.
You are especially inside it if you are in that awkward middle ground: too serious for consumer gear, too cost-conscious to leap straight into a heavier enterprise stack, and too tired to keep solving edge friction with workarounds.
The USG FLEX 200H was built for that band. Zyxel itself frames it around small business requirements, optional Nebula management, and essential security services, while listing the bundled 200H at a 2025 street price of $549.99 and the hardware-only unit at $399.99 in its U.S. launch update.
Where Wrong-Fit Begins
This is where calm honesty matters.
The 200H is not logical for everyone.
Wrong-fit starts in any of these situations:
Wrong-fit signal
Why this becomes regret
- You just need a basic router/firewall for a very small, light network
- You will pay for capability you will not metabolize
- You dislike licensing layers on principle
- The Gold bundle adds real value, but the category still has subscription logic
- You need every legacy Zyxel feature fully mature right now
- Community threads show H-series features have been arriving in stages
- You want zero learning curve
- Even positive reviews mention complexity and setup depth
- You are trying to solve Wi-Fi coverage, switching, and firewalling with one emotional purchase
- This product fixes the edge. It does not replace network design
There is another wrong-fit that buyers rarely admit: some people do not actually want control. They want the appearance of control without the burden of understanding. This is not the right machine for that mindset.

The One Situation Where This Product Becomes Logical
Here it is.
The Zyxel USG FLEX 200H becomes logical when your network edge has crossed from connectivity into enforcement.
That is the moment.
When you need the firewall to do more than sit there. When you want inspection active, not imagined. When multi-gig connectivity is no longer vanity. When VPN is part of normal life. When a few dozen users can still generate enough complexity to expose a weak edge in very expensive little ways.
This is why the 200H stands out more as a threshold appliance than a “best firewall” trophy. On paper it brings the right shape of headroom: 6.5 Gbps SPI throughput, 1.8 Gbps UTM throughput, 1.2 Gbps VPN, two 2.5GbE ports, six 1GbE ports, fanless design, and Nebula/cloud-management options. Third-party testing coverage around the sibling 200HP variant also points to strong thermal behavior, solid stress handling, local plus cloud manageability, and roughly one-second failover behavior in a dual-WAN scenario, which supports the broader H-series positioning even if that specific review is for the PoE sibling rather than this exact bundle.
That distinction matters. I am not smearing the models together. I am saying the hardware family consistently points in one direction: Zyxel was trying to fix the exact place where older SMB edge logic starts to feel thin.
What It Solves, What It Reduces, and What It Still Leaves to You
What it solves:
- the feeling that enabling real security will quietly punish performance,
- the edge bottleneck that makes faster WAN feel strangely underused,
- the awkward compromise between local control and centralized visibility,
- the need for a firewall that can sit in a serious small-business environment without acting embarrassed by it.
What it reduces:
- the likelihood that your security stack remains partly disabled out of fear,
- the administrative drag of managing a growing edge with too little headroom,
- the chance that remote access becomes the first thing everyone blames,
- the temptation to keep “making do” with equipment chosen for yesterday’s traffic profile.
What it still leaves to you:
- the licensing decision,
- the policy design,
- the learning curve,
- the responsibility to know whether your environment really belongs in this class.
This is not a magic amulet. It is a better boundary device.
And yes, the cautions are real. Community threads show feature gaps in early H-series development and individual cases of issues like reboot complaints or missing functions, while reviewer commentary also flags licensing complexity and a maturing cloud feature set. None of that cancels the product. It just keeps the article honest, which is the only kind of persuasion worth trusting.
Final Compression
Most firewall mistakes are not made because the buyer ignored security.
They are made because the buyer underestimated when security starts costing performance, attention, and certainty.
That is the line the Zyxel USG FLEX 200H is built to defend.
If your office is still genuinely light, this is probably more machine than you need. If you hate licensing, feature maturity curves, or admin depth, you should not pretend otherwise. But if you are already inside the threshold—multi-gig internet, real inspection, VPN usage, segmented traffic, and growing intolerance for edge friction—then the decision stops being abstract.
It becomes structural.
And once you can name the threshold, the cheap option usually stops looking cheap.
Transparency Note:
This analysis is built on aggregated real-world experience.
It extracts what repeatedly holds, what breaks, and what users uncover only after living with the system—then shapes it into a clear model you can use immediately.
Think of it as structured experience, refined and presented so you don’t have to learn it the hard way.
“A quick note: Don’t believe the star ratings, but trust personal experience. This article is a compilation of collected experiences”





